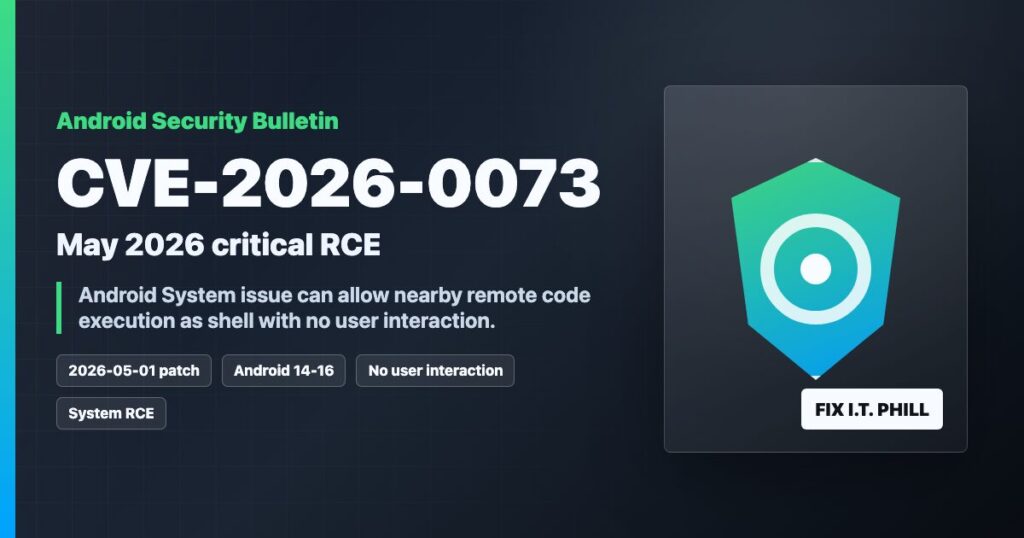
Impact statement: CVE-2026-0073 is the Android May 2026 issue to pay attention to. Google lists it as a critical System component remote code execution vulnerability. The official bulletin says user interaction is not needed and the vulnerable path can lead to code execution as the shell user.
The practical takeaway is simple: phones, tablets, kiosks, rugged Android devices, and fleet-managed Android endpoints should be moved to the 2026-05-01 security patch level or newer as fast as the vendor provides it.
What Makes This Different
This is not a normal “install a bad app and get hurt” warning. The Android bulletin describes CVE-2026-0073 as a remote proximal or adjacent code execution issue with no user interaction required. In plain English, the risk model includes nearby attack paths such as local wireless or adjacent-network exposure, depending on the device and enabled components.
Google lists the updated AOSP versions as Android 14, 15, 16, and 16-qpr2, and the bulletin also references Google Play system update coverage for the affected subcomponent.
Check A Device
On the device, open Settings, then check Security & privacy, System update, and Google Play system update. Exact menu names vary by manufacturer, but the security patch level should read May 1, 2026 or later.
For managed devices or lab verification with ADB:
adb shell getprop ro.build.version.security_patch
adb shell getprop ro.build.version.release
adb shell getprop ro.build.version.incremental
adb shell getprop ro.product.manufacturer
adb shell getprop ro.product.model
Admin Checklist
- Prioritize Pixel, Samsung, enterprise-owned, kiosk, MDM-managed, and BYOD devices that connect to company Wi-Fi or VPN.
- Install the May 2026 Android security update when the OEM offers it.
- Run the Google Play system update separately, then reboot.
- Temporarily reduce exposure for unpatched devices: avoid unknown Wi-Fi, disable developer options/ADB when not needed, and keep Bluetooth/Nearby Sharing off where practical.
- Track vendor lag. Some Android devices receive Google bulletin fixes later through OEM updates, carrier builds, or fleet policy windows.
For MDM And Fleet Owners
Set a compliance rule for security patch level 2026-05-01 or newer once your supported models have updates available. If a model cannot receive the update, decide whether it should keep accessing sensitive email, VPN, Wi-Fi, password managers, and internal apps.
Source Links
- Official Android Security Bulletin for May 2026
- Google guidance for checking and updating Android
- Pixel Update Bulletin for May 2026
Bottom Line
If an Android device can take the May 2026 security update, install it. If it cannot, reduce nearby-network exposure and keep it away from sensitive work until the device maker catches up.