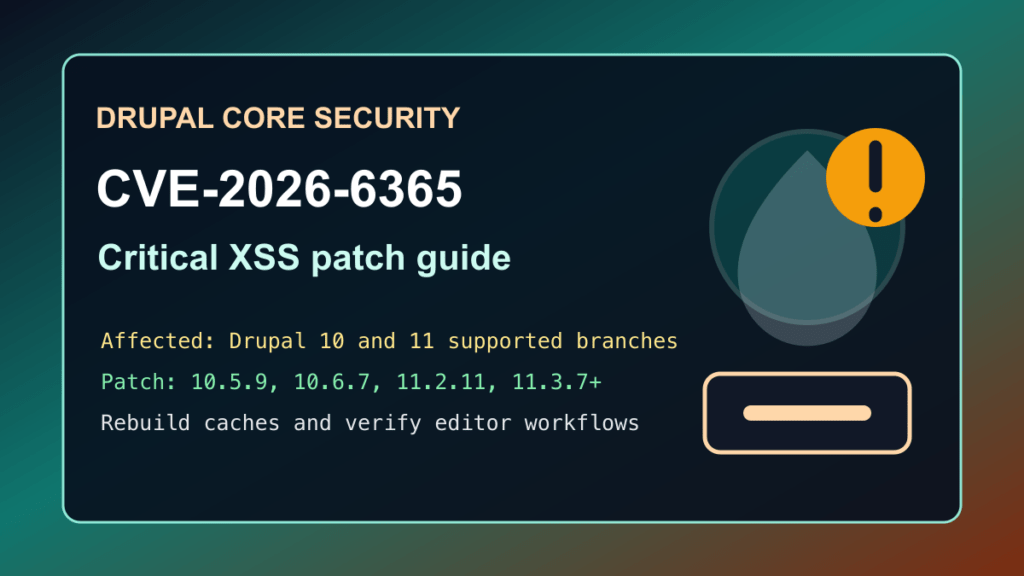
Drupal site owners should verify core updates for CVE-2026-6365. Drupal published SA-CORE-2026-001 for a critical cross-site scripting issue in Drupal core’s jQuery integration for AJAX modal dialog boxes. The affected ranges include supported Drupal 10 and 11 branches before the listed security releases.
This is a protect-only guide. Fix I.T. Phill is keeping the public guidance focused on defensive administration, update planning, cache rebuilds, and customer communication. The practical job is to identify Drupal core versions, apply the correct supported security release, and review sites that allow content editing, account workflows, or administrative modal dialogs.
Who is affected
Check every Drupal site, not just sites with contributed modules. This is a Drupal core advisory, so agencies, hosting providers, universities, nonprofits, membership sites, intranets, customer portals, and commerce sites should all verify their active core branch.
| Drupal branch | Affected versions | Fixed version |
|---|---|---|
| Drupal 10.5.x | 10.5.8 and older | 10.5.9 |
| Drupal 10.6.x | 10.6.6 and older | 10.6.7 or newer |
| Drupal 11.2.x | 11.2.10 and older | 11.2.11 |
| Drupal 11.3.x | 11.3.6 and older | 11.3.7 or newer |
Drupal also notes that Drupal 11.1.x, Drupal 11.0.x, Drupal 10.4.x and older are end-of-life for security coverage. Drupal 8 and Drupal 9 are also end-of-life. Sites on those branches should move to a supported branch instead of only trying to patch around the issue.
Plain-English impact
Cross-site scripting means attacker-controlled script can run in a visitor’s browser if the vulnerable condition is reached. In Drupal administration and content workflows, that can become serious because editors, moderators, and administrators often have sessions with higher privileges than normal visitors.
Drupal rates SA-CORE-2026-001 as critical. The advisory says the access complexity is high, but no account is required and all module configurations are considered exposed by Drupal’s target-distribution scoring. That combination makes this worth patching promptly even if a site does not appear to use a complex custom build.
What to update
Use Composer where the site is Composer-managed. Back up the site and database first, patch staging if the site has custom code or commerce workflows, then deploy the same dependency update through the normal release process.
composer show drupal/core-recommended
composer update "drupal/core-*" --with-all-dependencies
drush updatedb
drush cache:rebuildIf your deployment pins Drupal core to a specific release, update to the fixed release for your branch, then commit the changed Composer files and deploy from source control so the old vulnerable core is not restored later.
Safe verification checklist
- Confirm the active Drupal core branch and exact version.
- Confirm the site is on 10.5.9, 10.6.7, 11.2.11, 11.3.7, or a newer supported release.
- Run Drupal database updates after the Composer update.
- Rebuild caches and verify anonymous pages, editor login, content editing, media dialogs, checkout or donation flows, and customer-account workflows.
- Check that the production deployment source matches the patched code, especially on cPanel, Plesk, Git, and agency-managed sites.
drush status
drush updatedb:status
drush cache:rebuildIf you cannot patch immediately
The correct fix is to update Drupal core. Temporary controls can reduce risk while a maintenance window is prepared, but they should not become the permanent answer.
- Restrict administrative and editor access to trusted networks where possible.
- Pause risky content changes until the update is deployed on high-value sites.
- Use CDN/WAF challenge mode for suspicious traffic to editor, account, and content workflows if the customer approves it.
- Review whether old Drupal 8, Drupal 9, Drupal 10.4, Drupal 11.0, or Drupal 11.1 sites need an upgrade project instead of a routine patch ticket.
What logs and content to review
For sites that were exposed before patching, review web logs, WAF events, CMS logs, and recent content changes around editor workflows, forms, modal dialogs, media selection, account pages, and administrative sessions. Look for unusual anonymous traffic spikes, unexpected content changes, unfamiliar administrator activity, or complaints about strange browser behavior.
Keep incident notes sanitized. Do not paste customer data, cookies, form contents, or private page output into tickets unless the incident response process requires it.
Hosting and agency guidance
For Drupal fleets, search Composer lock files, deployment manifests, control-panel installs, and maintenance inventories for Drupal core branches. Prioritize unsupported branches, public customer portals, login-heavy sites, e-commerce or donation sites, and any site where editors or administrators work daily in the browser.
Customer communication can be direct: Drupal core has a critical security update for CVE-2026-6365. The site should be updated to a supported fixed core release, caches should be rebuilt, and common site workflows should be checked after deployment.
CDN and virtual patching note
Virtual patching can help buy time for exposed sites, but it does not replace the Drupal core update. For Help4 CDN-managed customers, the useful action is to identify Drupal sites that are not on a fixed supported release, raise protection on approved high-risk workflows during the maintenance window, and remove temporary restrictions after the core update is verified.
Bottom line
If a site runs Drupal 10 or 11, check the exact branch now. Update Drupal 10.5.x to 10.5.9, 10.6.x to 10.6.7 or newer, 11.2.x to 11.2.11, or 11.3.x to 11.3.7 or newer. Unsupported Drupal branches need an upgrade plan, not just a temporary mitigation.