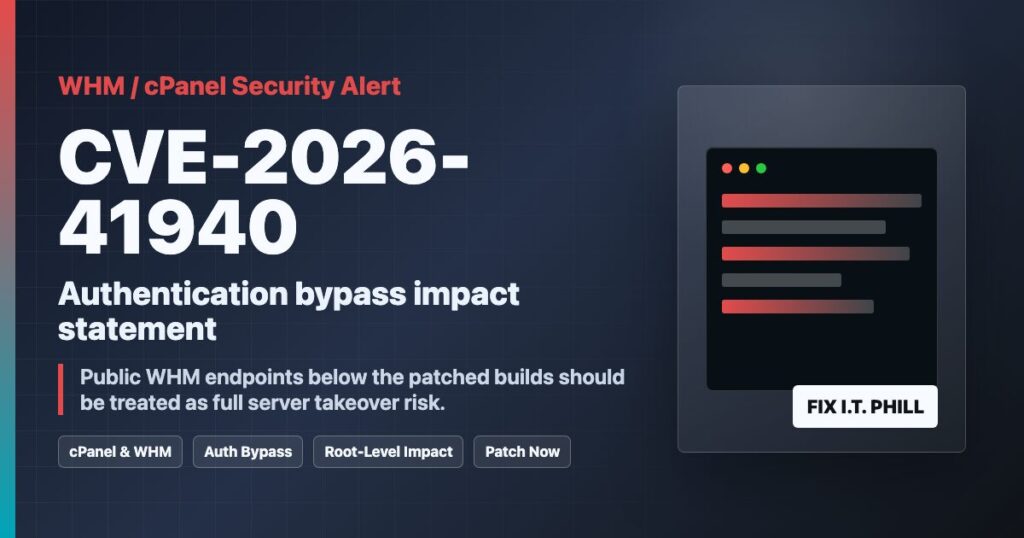
This is the one cPanel and WHM server owners should not sleep on.
Impact statement: If your WHM, cPanel, Webmail, or DNSOnly service was internet-facing and below the fixed builds listed by cPanel, treat CVE-2026-41940 as a potential full hosting-server compromise. This is not “one website got hacked.” This is the control panel layer that can affect every hosted site, mailbox, database, DNS zone, account backup, and reseller customer on that server.
What CVE-2026-41940 Is
cPanel describes CVE-2026-41940 as an authentication bypass affecting cPanel software, including DNSOnly, across versions after 11.40. In plain English: an attacker may be able to get into paths that should require authentication without first having a valid login.
For a WHM host, the practical risk is control-panel compromise that can affect hosted sites, mailboxes, DNS zones, backups, and reseller accounts. Patch first, then run cPanel’s official indicator checks.
Why The Impact Is So High
- WHM is the blast radius. A compromised WHM service can expose multiple cPanel accounts, not just one site.
- Shared hosting multiplies the damage. One exploited control-plane host can put many unrelated customers at risk.
- Email and databases matter. Attackers are not limited to public web files. Mailboxes, database dumps, DNS records, cron jobs, and backups are all sensitive.
- Credential cleanup is not optional. If exploitation indicators are present, assume passwords, API tokens, SSH keys, and application secrets may need rotation.
Who Needs To Worry
You should act immediately if you operate any of the following:
- A WHM/cPanel server with ports such as 2082, 2083, 2086, 2087, 2095, or 2096 exposed to the internet.
- A reseller hosting node, shared hosting node, agency hosting node, or customer cPanel platform.
- cPanel DNSOnly infrastructure.
- WP Squared instances listed in the cPanel advisory.
- Unsupported or frozen cPanel builds that cannot receive the emergency update.
Patched Versions Listed By cPanel
cPanel’s advisory lists fixed cPanel & WHM builds including:
- 11.110.0.97
- 11.118.0.63
- 11.126.0.54
- 11.130.0.18
- 11.132.0.29
- 11.134.0.20
- 11.136.0.5
cPanel also lists WP Squared 136.1.7 as patched. Use cPanel’s advisory as the authority because their supported build list is what matters operationally.
What Server Owners Should Do Now
- Update immediately. cPanel recommends updating to a fixed build with the cPanel update script. On WHM/cPanel servers that usually means running
/scripts/upcp --forceas root. - Confirm the version after the update. Do not assume the update completed because it started.
- Run the detection guidance from cPanel. Their CVE article includes an IOC detection script and required action notes.
- Review sessions, WHM users, API tokens, SSH keys, cron jobs, and recent file changes. If the server shows compromise indicators, the response is bigger than just patching.
- Force credential rotation if indicators are found. That includes root, WHM users, reseller accounts, cPanel users, database users, application secrets, and any tokens stored on the host.
- Isolate if patching fails. If the server cannot update cleanly, reduce public exposure to WHM/cPanel/Webmail ports until it can be patched and verified.
What Website Owners Should Ask Their Host
If you are on shared hosting, you may not have WHM root access. That does not mean the issue is irrelevant. Ask your provider these direct questions:
- Was my hosting node affected by CVE-2026-41940?
- What cPanel & WHM build is the server running now?
- Did you run the cPanel IOC detection script?
- Were any unauthorized sessions, WHM users, API tokens, or file changes found?
- Do I need to rotate my cPanel, email, FTP, database, and application passwords?
Source Links
- cPanel advisory for CVE-2026-41940
- cPanel & WHM security update notes
- Rapid7 analysis of CVE-2026-41940
- R-fx Networks reverse-engineering write-up
- CISA Known Exploited Vulnerabilities catalog
Bottom Line
If you run WHM/cPanel, this is a patch-now and verify-now event. If you host customers, this is also a communication event. People trust you with their websites, email, and customer data. Give them straight answers, confirm the server is patched, and do not skip the compromise checks.
Need help checking a cPanel server or cleaning up after suspicious activity? Open a ticket through Help4Network.com.