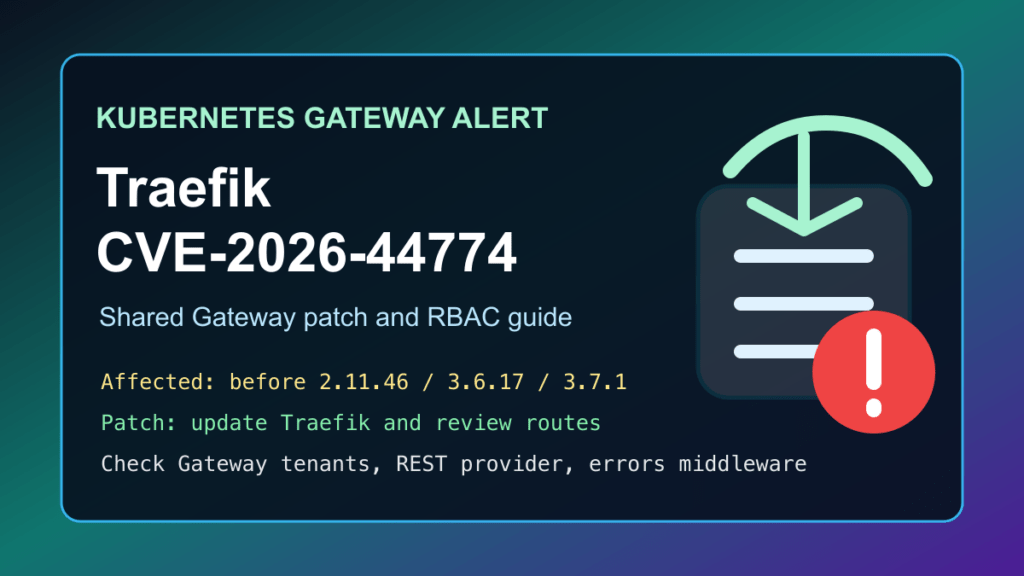
Traefik users running shared Kubernetes Gateway environments should patch CVE-2026-44774 now. The issue affects Traefik before 2.11.46, 3.6.17, and 3.7.1. In the risky configuration, a lower-privileged tenant who can create Gateway routes may be able to cross an internal Traefik trust boundary when the REST provider is enabled.
This is a protect-only guide. Fix I.T. Phill is not publishing route recipes, internal service names, request examples, or scanner-ready details. The useful part for defenders is to identify affected Traefik versions, check whether the risky Gateway and REST-provider combination exists, update Traefik, and tighten tenant route permissions.
Who Should Check
- Kubernetes clusters using Traefik as an ingress, edge proxy, or Gateway API controller.
- Shared clusters where application teams, customers, or tenants can create HTTPRoute resources.
- Hosting providers, SaaS platforms, DevOps teams, agencies, and MSPs that run many customer workloads behind one Traefik deployment.
- Docker, Kubernetes, and GitOps environments where Traefik images are pinned and may not update automatically.
- Sites using Traefik custom error pages, because CVE-2026-41181 is a related credential-handling issue worth patching at the same time.
Affected Versions And Fixes
| CVE | Risk | Affected versions | Fixed versions | When it matters most |
|---|---|---|---|---|
| CVE-2026-44774 | Kubernetes Gateway trust-boundary bypass | 2.11.45 and older, 3.6.16 and older, 3.7.0 and older | 2.11.46, 3.6.17, 3.7.1 or newer | Shared Gateway deployments with the REST provider enabled and tenant route creation allowed |
| CVE-2026-41181 | Sensitive header forwarding to a separate error-page service | 2.11.43 and older, 3.6.14 and older, 3.7.0-rc.2 and older | 2.11.44, 3.6.15, 3.7.0-rc.3 or newer | Deployments using Traefik custom error pages backed by a separate service |
If you are already moving versions, target 2.11.46, 3.6.17, 3.7.1, or newer so both Traefik issues are covered by one maintenance plan.
Plain-English Impact
CVE-2026-44774 is not an unauthenticated internet-wide Traefik bug. It depends on a specific shared Kubernetes Gateway design. The concern is that someone with limited route-authoring access may be able to reach an internal dynamic configuration surface when the REST provider is enabled. In a multi-tenant cluster, that can turn a normal application-routing permission into a way to change Traefik routing behavior.
CVE-2026-41181 is different: it affects custom error-page handling. In affected versions, a separate error-page service may receive more request headers than operators expect, including sensitive authentication material. That matters if the error-page service is managed by a different team, logs aggressively, or has weaker access controls than the original backend.
Safe Version Checks
Check the Traefik version from the running container, Helm release, GitOps values, or deployment image tag. These are inventory checks only. They do not attempt to validate the vulnerability.
traefik version kubectl -n traefik get deploy -o wide helm -n traefik list helm -n traefik get values traefik
If your namespace is not named traefik, use the namespace where your Traefik release is installed. Also check CI/CD manifests, Argo CD, Flux, Terraform, Ansible, and image-pinning rules so the fixed version does not get rolled back later.
Patch Checklist
- Export the current Helm values, Kubernetes manifests, and Traefik static configuration before changing anything.
- Schedule a maintenance window for production clusters, especially if Traefik terminates TLS or fronts customer traffic.
- Update Traefik to 2.11.46, 3.6.17, 3.7.1, or a newer vendor-fixed release.
- Confirm that the intended Traefik image tag is running after the rollout finishes.
- Restrict route creation and route attachment rights to the smallest set of namespaces and teams that genuinely need them.
- Disable the REST provider unless you have a documented operational need for it.
- Review custom error-page services and reduce sensitive logging on any service that receives error-rendering traffic.
- Clear relevant CDN, edge, and application caches only after verifying that traffic is flowing through the updated Traefik pods.
Cluster-Safe Rollout Guidance
For a single Traefik deployment, use a rolling update and watch readiness, service endpoints, and ingress health. For larger clusters, drain traffic gradually: update staging first, update one production cluster or region, watch error rates and latency, then continue. If Traefik is part of a high-availability edge layer, keep at least one healthy instance serving traffic while the next one rolls.
After the update, test representative routes for normal pages, APIs, TLS redirects, WebSocket or gRPC traffic, uploads, login flows, and custom error pages. A clean security update still needs application-level smoke testing because Traefik often sits directly in front of customer-facing workflows.
What To Review After Patching
- Recent Gateway and HTTPRoute changes in tenant namespaces.
- Unexpected Traefik dynamic configuration changes, new routers, new services, or unusual provider activity.
- Traefik access logs, Kubernetes audit logs, GitOps commit history, and admission-controller events.
- Custom error-page service logs for sensitive authorization headers, session cookies, or customer identifiers.
- Namespaces where non-platform teams can attach routes to shared Gateways.
- Any automation that grants broad route creation rights to CI jobs, deployment bots, or customer self-service tools.
Temporary Mitigation
Updating Traefik is the real fix. If you cannot update immediately, temporarily reduce the blast radius: disable the REST provider if it is not required, restrict who can create or modify Gateway routes, narrow allowed route attachment by namespace, and add admission policy checks for internal service references. For custom error pages, keep error-page services under the same trust boundary as the protected app or strip sensitive headers before requests leave that boundary.
For hosting providers and MSPs, prioritize clusters where multiple customers or multiple application teams share one Gateway. Single-tenant clusters are still worth patching, but shared routing control planes carry the bigger business risk.
Customer Communication
Keep customer notes plain: Traefik released security updates, the cluster was checked for the affected configuration, the proxy was updated or scheduled for update, and route permissions were reviewed. Do not send customers the internal service names or request examples behind the advisory. Tell them what was patched, what was reviewed, and whether any application smoke testing is needed from their side.
Fix I.T. Phill CDN/WAF Note
We are leaving a sanitized note for the Help4 CDN side to review whether any customer-facing Traefik admin, dashboard, REST, or internal-routing surfaces are exposed through CDN-managed hostnames. Virtual patching can help with exposed management paths, but it does not replace the Traefik update or Kubernetes RBAC cleanup inside the cluster.